12.16.198.1100: System Traffic Analysis
System traffic analysis has become essential for organizations seeking to bolster cybersecurity and improve network performance. By monitoring IP traffic, businesses can detect anomalies and optimize resources. This analytical approach not only reduces potential threats but also enhances overall infrastructure resilience. Understanding the nuances of traffic patterns can reveal critical insights. What strategies can organizations implement to fully leverage these insights for greater security and efficiency?
Understanding the Importance of IP Traffic Analysis
Although many organizations recognize the necessity of monitoring network performance, the significance of IP traffic analysis extends beyond mere performance metrics.
By examining IP behavior and identifying traffic patterns, entities can enhance security, optimize resource allocation, and ensure compliance with regulations.
This analysis provides insights into user activities, helping to mitigate risks and foster a more resilient network infrastructure, ultimately promoting a culture of digital freedom.
Methods for Analyzing System Traffic
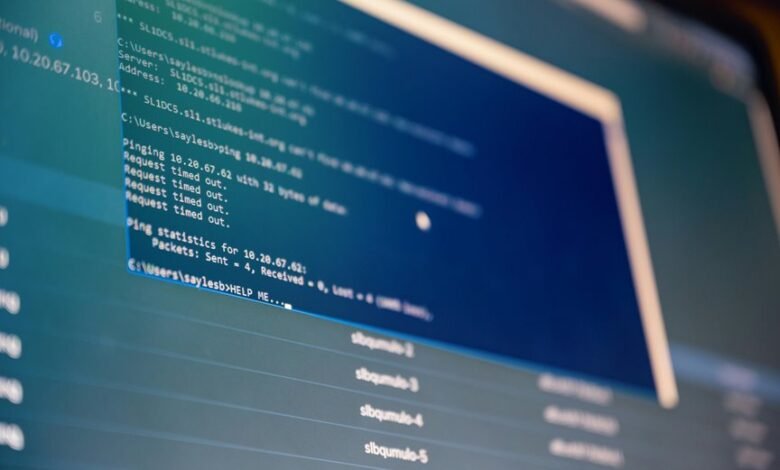
Analyzing system traffic involves a variety of methodologies that facilitate the identification and interpretation of network data flows.
Techniques such as packet inspection allow for detailed examination of transmitted data, enabling the detection of network anomalies.
Enhancing Cybersecurity Through Traffic Insights
Understanding the intricacies of system traffic can significantly bolster an organization’s cybersecurity posture.
By analyzing traffic patterns, organizations can identify deviations indicative of potential threats. Anomaly detection techniques play a crucial role in this process, enabling proactive responses to unusual behavior.
This analytical approach not only enhances overall security but also promotes a resilient infrastructure, ensuring the freedom and integrity of digital operations.
Conclusion
In conclusion, system traffic analysis is indispensable for modern organizations seeking to bolster cybersecurity and optimize network performance. While some may argue that the implementation of such monitoring systems is resource-intensive, the long-term benefits—including enhanced threat detection and improved operational efficiency—far outweigh the initial investment. By embracing a proactive approach to traffic analysis, organizations can not only safeguard their digital assets but also ensure a robust infrastructure capable of adapting to evolving cyber threats.





